Your Data May Already Be Stolen
Adversaries playing the long game are harvesting data now, waiting until quantum computers mature enough to crack the encryption.
The assumption that quantum computers capable of breaking encryption are still decades away is no longer valid. Recent advances have moved the cryptographic breakthrough timeline forward to just a few years from now. Bill Sparks examines what this means for data security.
The Quantum Threat
Somewhere right now, on servers controlled by a foreign intelligence service, there are terabytes of encrypted corporate data. Financial records. Strategic plans. Customer information. Merger negotiations. Legal communications. All of it was intercepted over the past several years as it moved across the internet. None of it can be read today. The encryption protecting it is, by current standards, unbreakable.
But someone is keeping it. And they're waiting for a machine that can break it open.
The cybersecurity community has a name for this. They call it "harvest now, decrypt later." The concept is disturbingly simple. Adversaries, mostly nation-states with the resources and patience to play long games, are vacuuming up vast quantities of encrypted data and storing it. They can't read it yet. They don't need to. They just need to hold onto it until quantum computers mature enough to crack the encryption. At that point, everything they've collected becomes an open book.
Doug Adams of Vanderbilt's Institute of National Security described the situation at the Vanderbilt Quantum Forum in April 2026. "They're capturing the data and they're waiting. They're very patient."
The uncomfortable implication for business leaders is that the timeline of a data breach has been turned upside down. The theft happens now. The damage happens later. And by the time you know about it, there's nothing you can do.
A Non-Technical Explanation of Why This Is Possible
To understand why quantum computing is such a threat to encryption, it helps to understand what makes it different from the computers we use every day.
A conventional computer processes information using bits, which are tiny switches that are either on or off, either a 1 or a 0. Every calculation a computer performs, no matter how complex, is built from long sequences of these binary choices. When a conventional computer encounters a problem with many possible solutions, it essentially tries them one at a time. It's very fast at this, but it's still working through the options sequentially, like trying every possible combination on a padlock by hand. For a sufficiently complex problem, even the fastest conventional computer would take longer than the age of the universe to find the answer.
This is exactly how modern encryption works. It's based on mathematical problems that are easy to create but practically impossible to solve by brute force. The most common form, called RSA encryption, relies on the difficulty of factoring extremely large numbers into their prime components. A conventional computer simply can't do it in any useful timeframe. That's what makes your data "secure."
A quantum computer is a fundamentally different kind of machine. Instead of bits that are either 1 or 0, it uses "qubits" that can exist in multiple states simultaneously through a property of quantum physics called superposition. Qubits can also be entangled with one another, meaning the state of one instantly influences the state of another. The practical result is that a quantum computer doesn't try solutions one at a time. It can explore vast numbers of possibilities in parallel.
In 1994, a mathematician named Peter Shor demonstrated that a sufficiently powerful quantum computer running the right algorithm could factor those enormous numbers that RSA encryption depends on. Not in a billion years. In hours. When that machine arrives, the mathematical lock on which virtually all internet security depends will simply stop working. Not just for future data, but for every piece of encrypted data that has ever been collected by anyone.
That's what makes harvest now, decrypt later so dangerous. The data you think is safe, is only safe for now.
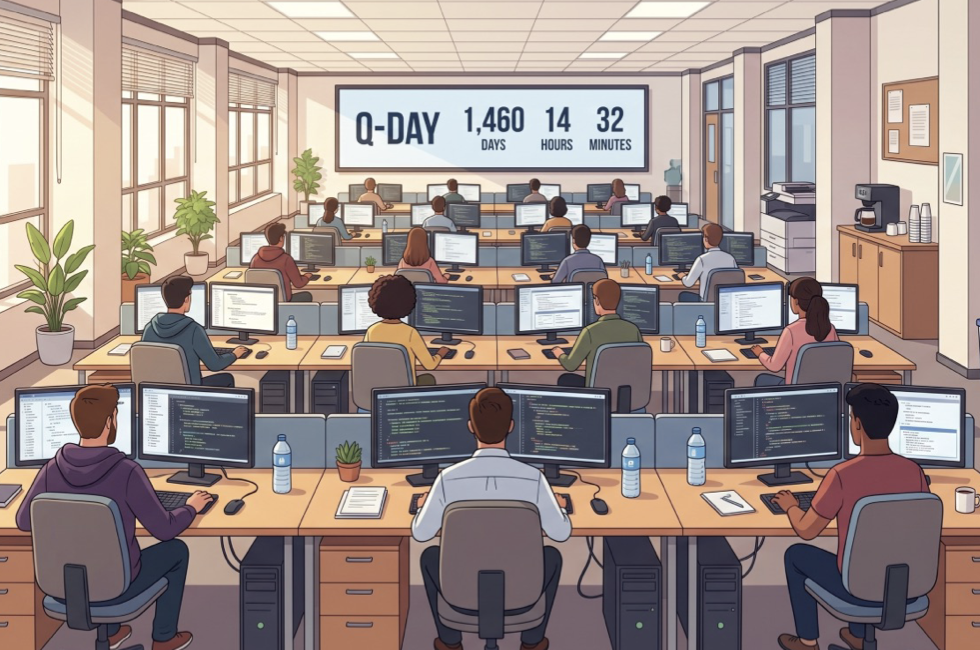
The Cloud Security Alliance estimates that "Q-Day," the day a quantum computer can break current encryption, could arrive by 2030. The companies closest to the problem are moving fast to deal with the threat.
How Close Is This, Really?
The comfortable assumption for many executives has been that quantum computers capable of breaking encryption are still decades away. That assumption is no longer safe.
The timeline has been compressing at a pace that has surprised even the experts. In 2019, researchers estimated that breaking standard RSA-2048 encryption would require a quantum computer with approximately 20 million physical qubits. By 2025, improved algorithms and architectures had dropped that estimate to under one million. By early 2026, some researchers were suggesting it could be done with as few as 100,000 qubits under certain conditions.
Google recently accelerated its own internal deadline for migrating to quantum-resistant encryption from a vague "eventually" to a firm 2029, citing faster-than-expected advances in quantum hardware and error correction. Cloudflare, which handles a large percentage of global internet traffic, is targeting 2029 for full post-quantum security. IonQ, one of the leading quantum hardware companies, has published a roadmap targeting cryptographically relevant quantum capabilities as early as 2028.
The Cloud Security Alliance estimates that "Q-Day" — the day a quantum computer can break RSA-2048 — could arrive by 2030. That's four years from now. The people who build these machines are moving their own deadlines forward. That should tell you everything you need to know about whether this is still a "future" problem.
Are You Already Too Late?
Dr. Michele Mosca, a cryptography researcher at the University of Waterloo, developed a formula that makes the risk concrete even for non-technical leaders. It's called Mosca's Theorem, and it works like this.
If the number of years your data needs to stay secret (X), plus the number of years it will take your organization to migrate to quantum-safe encryption (Y), is greater than the number of years until a quantum computer can break your current encryption (Z), then your data is already at risk. If X + Y is greater than Z, you're too late.
Here's what the math looks like for a typical large enterprise. Customer financial records that need to remain confidential for 15 years. A realistic cryptographic migration timeline of 8 to 12 years for a large organization. A Q-Day estimate of 4 to 9 years from now.
X + Y = 23 years on the low end. Z = as little as 4. The equation is already deep in the red for most large organizations. If you haven't started migrating, you're not early. You may already be late.
Who's Already Moving
The companies closest to the quantum problem are moving fastest. That itself is a signal worth paying attention to.
Apple integrated post-quantum encryption into iMessage in early 2024 through a protocol called PQ3, and has since expanded quantum-resistant protections across iOS 26, iPadOS 26, and macOS. As of April 2026, more than 65% of all human-initiated traffic on Cloudflare's network is already protected using post-quantum methods. Microsoft has made post-quantum cryptography APIs available in Windows Server 2025 and Windows 11. Google has set a firm 2029 deadline for migrating its entire product ecosystem to quantum-resistant encryption.
On the regulatory side, the movement is just as urgent. NIST finalized its first three post-quantum cryptography standards in August 2024 after an eight-year development process and has stated plainly that organizations should begin applying them now. The NSA's CNSA 2.0 directive mandates that all new National Security Systems acquisitions be post-quantum compliant by January 2027, with full compliance required by 2033. The European Commission has directed organizations to begin transitioning by the end of 2026.
The Boston Consulting Group put it bluntly: "Starting in 2030 will already be too late."
The gap between the companies that are acting and the companies that aren't is the core risk this article is about. If the biggest and most technically sophisticated organizations in the world are treating this as urgent, the question for everyone else is: what do they know that you don't?
What to Do About It
The good news is that you don't need to understand quantum physics to take the right steps. You need to understand your own data and your own timelines.
First, figure out what you're protecting and for how long. Before you can assess your quantum risk, you need to know what data you hold, how long it needs to remain confidential, and where it lives. This is the X in Mosca's equation. Most companies have never done this exercise. It's not glamorous work, but it's the foundation for everything that follows.
Second, run Mosca's math for your organization. Plug in your numbers. How long does your most sensitive data need to stay secret? How long would a full cryptographic migration realistically take given your systems, your budget, and your technical debt? Compare that total against the most credible Q-Day estimates. If X + Y is greater than Z, you have a problem that is already active, not theoretical.
Third, build systems that can adapt. The goal right now is not to predict exactly which encryption standard will dominate in 2030. The goal is to build what cryptographers call "crypto-agility" — the ability to swap cryptographic protocols without having to tear your entire infrastructure apart. The organizations that build this flexibility now will be able to adopt new standards as they emerge without starting from scratch each time.
Fourth, start with your highest-value, longest-lived data. You don't need to migrate everything at once. Prioritize the data that combines high sensitivity with long confidentiality requirements: financial records, intellectual property, health data, strategic communications, anything related to government contracts. This is where harvest now, decrypt later poses the greatest risk and where migration delivers the most immediate value.
When encryption collapses, a problem that was invisible for years can suddenly appear with disastrous consequences.
The Breach You Can't See
The quantum threat is unlike any cybersecurity challenge most executives have encountered. There is no alarm when the breach happens. There is no ransom note. There is no system outage. The theft is silent, the data sits encrypted on someone else's server, and the damage is deferred by years. You may never even know it happened until the encryption collapses and your most sensitive information becomes readable by whoever was patient enough to collect it.
That's what makes it so dangerous. And that's what makes it so easy to ignore.
Apple, Google, Microsoft, and Cloudflare are not moving fast on post-quantum migration because they're naturally cautious organizations. They're moving because they understand the math. The question for every other business leader is straightforward: do you?
Facts and figures in this article are current as of May 4, 2026. Quantum computing capabilities and regulatory timelines are evolving rapidly.
The Advantage Journal arrives every week. What matters in sport, mobility, media, and technology — curated and contextualized by Bill Sparks, Bill Long, and Paul Pfanner. No hedging. No filler. Subscribe — It’s Free